Homeland Security Officially Blames North Korea for WannaCry Ransomware Outbreak
Posted by: Timothy Tibbetts on 12/19/2017 05:47 AM
[
 Comments
]
Comments
]
President Trump's Homeland Security Adviser Thomas Bossert has officially blamed North Korea for the WannaCry ransomware incident that crippled hundreds of thousands of computers worldwide in May.
"North Korea has acted especially badly, largely unchecked, for more than a decade, and its malicious behavior is growing more egregious. WannaCry was indiscriminately reckless," he added.
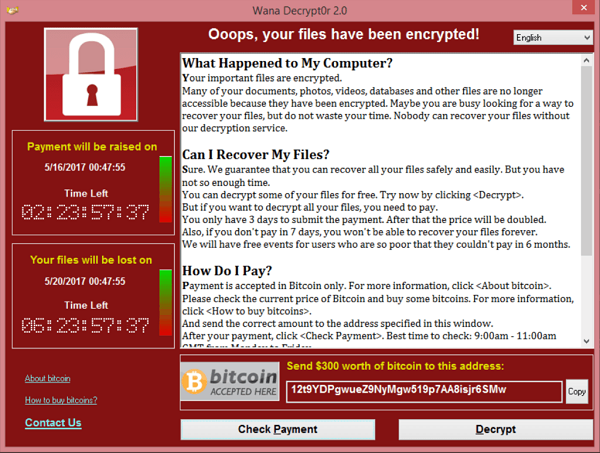
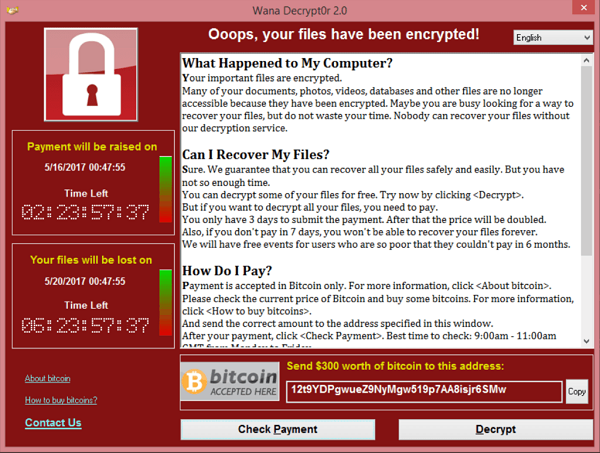
WannaCry was considered a payload, which works in the same fashion as most ransomware: it finds and encrypts a range of data files, then displays a ransom note informing the user and demanding a payment in bitcoin.
The attack began on Friday, 12 May 2017, and within a day was reported to have infected more than 230,000 computers in over 150 countries. After four days, the attacks slowed down.
WannaCry propagates using EternalBlue, an exploit of Windows' Server Message Block (SMB) protocol. A lot of attention was also given because the U.S. National Security Agency had already discovered the vulnerability, but used it to create an exploit for its own needs, rather than report it to Microsoft. Microsoft eventually discovered the vulnerability and made patches available.
"North Korea has acted especially badly, largely unchecked, for more than a decade, and its malicious behavior is growing more egregious. WannaCry was indiscriminately reckless," he added.
WannaCry was considered a payload, which works in the same fashion as most ransomware: it finds and encrypts a range of data files, then displays a ransom note informing the user and demanding a payment in bitcoin.
The attack began on Friday, 12 May 2017, and within a day was reported to have infected more than 230,000 computers in over 150 countries. After four days, the attacks slowed down.
WannaCry propagates using EternalBlue, an exploit of Windows' Server Message Block (SMB) protocol. A lot of attention was also given because the U.S. National Security Agency had already discovered the vulnerability, but used it to create an exploit for its own needs, rather than report it to Microsoft. Microsoft eventually discovered the vulnerability and made patches available.
Comments





