2 Million Facebook, Gmail, ADP, Yahoo! and Twitter passwords compromised
Posted by: Jon Ben-Mayor on 12/05/2013 04:41 AM
[
 Comments
]
Comments
]
Hackers have obtained an estimated 2 Million usernames and passwords from Facebook, Gmail, ADP, Twitter and Yahoo! - the breach was a result of keylogger tool that was installed on an unknown number of computers. The version of the malicious software being used is the Pony botnet controller.
With so much data in our hands, we thought it would be interesting to look into some statistics regarding this particular attack.
We’ll start off with the final numbers, and then break it down:
~1,580,000 website login credentials stolen
~320,000 email account credentials stolen
~41,000 FTP account credentials stolen
~3,000 Remote Desktop credentials stolen
~3,000 Secure Shell account credentials stolen
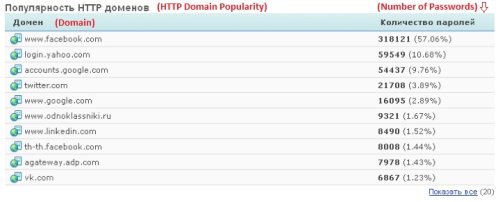
As one might expect, most of the compromised web log-ins belong to popular websites and services such as Facebook, Google, Yahoo, Twitter, LinkedIn, etc.
You can also spot the notable presence of vk.com and odnoklassniki.ru, two social network websites aimed at Russian-speaking audiences, which probably indicates that a decent portion of the victims comprised were Russian speakers. Another interesting item on the list is the payroll service provider adp.com. It is only natural to have such domains in the mix, but it is surprising to see it ranked #9 on the top domains list. Facebook accounts are a nice catch for cyber criminals, but payroll services accounts could actually have direct financial repercussions.
Trustwave has already notified the service providers prior to making the information public. In turn, Facebook and Twitter told CNNMoney they have since reset passwords for all of its compromised users. Google, Yahoo, ADP and LinkedIn did not provide immediate responses for comment.
John Miller, a security research manager at Trustwave said "We don't have evidence they logged into these accounts, but they probably did."
With so much data in our hands, we thought it would be interesting to look into some statistics regarding this particular attack.
We’ll start off with the final numbers, and then break it down:
~1,580,000 website login credentials stolen
~320,000 email account credentials stolen
~41,000 FTP account credentials stolen
~3,000 Remote Desktop credentials stolen
~3,000 Secure Shell account credentials stolen
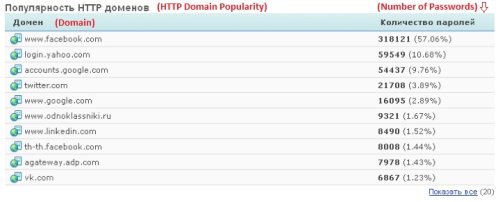
As one might expect, most of the compromised web log-ins belong to popular websites and services such as Facebook, Google, Yahoo, Twitter, LinkedIn, etc.
You can also spot the notable presence of vk.com and odnoklassniki.ru, two social network websites aimed at Russian-speaking audiences, which probably indicates that a decent portion of the victims comprised were Russian speakers. Another interesting item on the list is the payroll service provider adp.com. It is only natural to have such domains in the mix, but it is surprising to see it ranked #9 on the top domains list. Facebook accounts are a nice catch for cyber criminals, but payroll services accounts could actually have direct financial repercussions.
Trustwave has already notified the service providers prior to making the information public. In turn, Facebook and Twitter told CNNMoney they have since reset passwords for all of its compromised users. Google, Yahoo, ADP and LinkedIn did not provide immediate responses for comment.
John Miller, a security research manager at Trustwave said "We don't have evidence they logged into these accounts, but they probably did."
Comments





