Target ups number of customers affected to 110 Million as cybercriminals feverishly attempt to decrypt info
Posted by: Jon Ben-Mayor on 01/10/2014 01:26 PM
[
 Comments
]
Comments
]
Target has been methodically investigating the breach that occurred over the start of the Christmas holiday shopping season. The retailer has now revised the number of customers from the original 40 Million to approximately 110 Million unique customer records being affected.
In a press release, Dan Clements, President of IntelCrawler says "It seems the underground is in a race to try and decrypt the PIN's before banks can re-issue new cards."
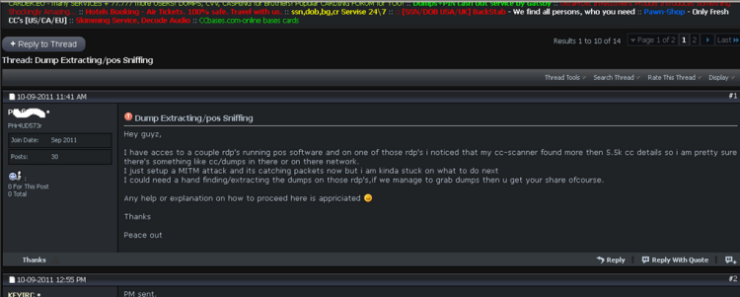
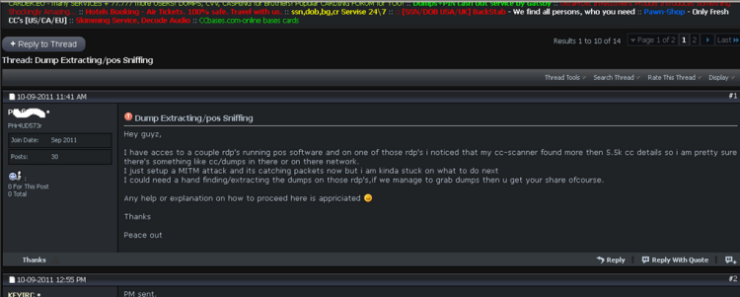
According to sources of IntelCrawler, there is an active group of Eastern European cybercriminals who specializes in attacks on merchants and Point-of-Sale terminals by using sophisticated malware and targeted perimeter attacks. Their goal is the interception of payment and PIN blocks data, which many systems have been sniffed and grabbed in the past. The recent request by the underground to decrypt PIN data, see below, may be co-incidental to the Target breach or possibly some of the actual perpetrators floating the sample to see what resources and success the power of the underground has had or could have given the magnitude and value of the target breach.
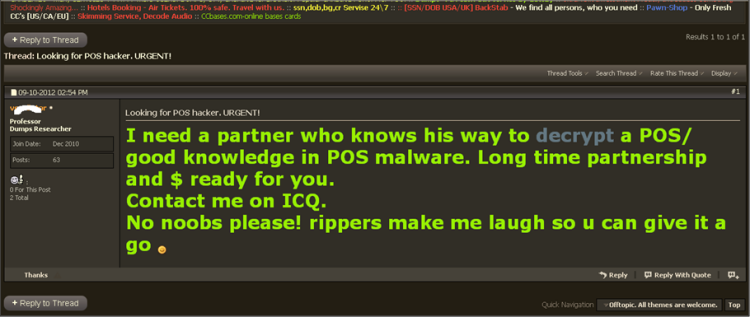
Just recently, several criminals in underground are interested in decrypting of 3DES blocks and information intercepted from serial COM-port connected to POS (9600 7E1) and Man-in-the-Middle attack.
It may be a slow process, but decrypting the 3DES encrypted PINs is entirely possible, Andrew Komarov, CEO at IntelCrawler, told SCMagazine.com on Wednesday. He explained that 3DES encryption may be vulnerable to brute-force and added that programs such as John the Ripper, a free password cracking tool, may facilitate the process.
Robert Graham from Errata Security explains further, let's say that the hacker shopped at Target before stealing the database. The hacker's own debit card information will be in the system. Let's say the hacker's PIN was 8473. Let's say that this encrypts to 98hasdHOUa. The hacker now knows that everyone with the encrypted PIN of "98hasdHOUa" has the same pin number as him/her, or "8473". Since there are only 10,000 combination of PIN numbers, the hacker has now cracked 1000 PIN numbers out of 10 million debit cards stolen.
This just gets one debit card. The hacker can crack the rest using the same property. The hacker simply starts at PIN number "0000", and then using online sites, starts using that number, trying one card at a time, until s/he gets a hit. On average, the hacker will have to try 10,000 before a good result is found. Once found, all debit cards with the same encrypted PIN of "0000" are moved aside to the "known" category. The hacker then repeats the process with "0001", "0002", and so on for all combinations.
In a press release, Dan Clements, President of IntelCrawler says "It seems the underground is in a race to try and decrypt the PIN's before banks can re-issue new cards."
According to sources of IntelCrawler, there is an active group of Eastern European cybercriminals who specializes in attacks on merchants and Point-of-Sale terminals by using sophisticated malware and targeted perimeter attacks. Their goal is the interception of payment and PIN blocks data, which many systems have been sniffed and grabbed in the past. The recent request by the underground to decrypt PIN data, see below, may be co-incidental to the Target breach or possibly some of the actual perpetrators floating the sample to see what resources and success the power of the underground has had or could have given the magnitude and value of the target breach.
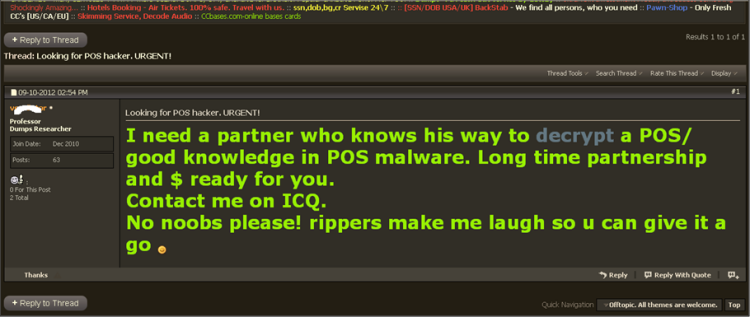
Just recently, several criminals in underground are interested in decrypting of 3DES blocks and information intercepted from serial COM-port connected to POS (9600 7E1) and Man-in-the-Middle attack.
It may be a slow process, but decrypting the 3DES encrypted PINs is entirely possible, Andrew Komarov, CEO at IntelCrawler, told SCMagazine.com on Wednesday. He explained that 3DES encryption may be vulnerable to brute-force and added that programs such as John the Ripper, a free password cracking tool, may facilitate the process.
Robert Graham from Errata Security explains further, let's say that the hacker shopped at Target before stealing the database. The hacker's own debit card information will be in the system. Let's say the hacker's PIN was 8473. Let's say that this encrypts to 98hasdHOUa. The hacker now knows that everyone with the encrypted PIN of "98hasdHOUa" has the same pin number as him/her, or "8473". Since there are only 10,000 combination of PIN numbers, the hacker has now cracked 1000 PIN numbers out of 10 million debit cards stolen.
This just gets one debit card. The hacker can crack the rest using the same property. The hacker simply starts at PIN number "0000", and then using online sites, starts using that number, trying one card at a time, until s/he gets a hit. On average, the hacker will have to try 10,000 before a good result is found. Once found, all debit cards with the same encrypted PIN of "0000" are moved aside to the "known" category. The hacker then repeats the process with "0001", "0002", and so on for all combinations.
Comments





