Types of Phishing Attacks and How to Spot Them
By Corporal Punishmenton 05/23/2023 |
 Hey Geeks!
Hey Geeks! Many of you may know what Phishing is - many do not.
Phishing is a cyberattack that uses fake emails, phone calls, text messages, or any other way you can be reached to trick you into giving up your personal information or account information. The name comes from 'fishing', implying to cast some bait out there and see who bites.
According to the FBI, Phishing is the most common threat to online security, with over 3.3 Billion in reported losses in 2022 alone. Also, according to Cisco, Phishing makes up over 90% of all data breaches on the internet.
With the increase in technology, to keep pace, Phishing attacks are also becoming increasingly sophisticated.
Recently in reaching out to a Twitter support account for a company we use, we had an obvious Phish response to our support request in seconds. Not minutes... Seconds. Way faster than the actual tech support staffers. It looked legit, too, though I doubt any reputable company would let their tech support use the handle, Mistress Astra. (#FirstClue) .. which prompted this article.
But Don't Panic! We are here to help you spot the difference between an actual contact and a phishing scam and hopefully save you some trouble. Here are the most common types. (I swear we didn't make up these names)
Deceptive Phishing
Deceptive Phishing is the most common phishing attack. This is when a scammer tries to impersonate a legitimate company or organization to get you to click on a link or provide your credentials. For example, you might receive an email from your bank asking you to verify your account or from a famous shopping site asking you to verify your recent order. These emails often create a sense of urgency or threat, making you act quickly and without thinking. When clicked, the link will usually look exactly like the website you are used to, giving you comfort, but if you look at the landing page URL, it will be wrong. For example, instead of 'Chase.com', it may be something like 'ChaseOnlineSite.org'
How to protect yourself against Deceptive Phishing:
- Legitimate companies will never email you your password or credit card number or request personal information.
- Look for spelling or grammar errors, generic greetings, or suspicious URLs. Most professional emails are proofread.
- Check the sender's address. For example, if the email claims to be from Microsoft, but the address is micr0s0ft@gmail.com, that's a red flag.
- Beware of urgent or threatening messages. Deceptive phishers often try to create a sense of urgency or fear to make you act quickly without thinking.
- Use common sense. Emails that offer gift cards, lottery prizes, or refunds for something you never bought are a scam.
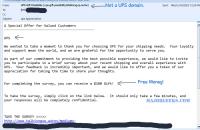
Spear Phishing
Spear phishing is a more targeted attack where scammers customize their emails to a specific individual or group. They use information from social media profiles or other sources to make their emails more convincing and personalized. For example, you might receive an email from your friend asking you to open an attachment - but if you look closely, the friend's email address is wrong. Or, I get a lot of mail from the MajorGeeks IT department asking me to sign in to my Webmail for "security." Since I AM the IT department, that's a red flag right there.
How to protect yourself against Spear Phishing:
- Be wary of emails that ask you for sensitive information or actions that seem out of character for the sender.
- Look at the actual return email address, not the name.
- Verify the sender's identity by calling or checking the validity of the request.
Whaling
Whaling is spear phishing that targets high-level executives, managers, or Whales. Scammers pretend to be someone in authority, such as the CEO, and ask for financial transfers, access to accounts, or sensitive data. These attacks can cause substantial losses and reputational damage to the organization. One classic example was in 2016 Snapchat, a miscreant impersonating the CEO was able to access company payroll data.
How to protect yourself against Whaling:
- Be suspicious of emails from senior executives or leaders that seem unusual or urgent.
- Check the sender's email address and domain name carefully.
- When in doubt, call or text the person who sent you the email to verify if it's really them. Don't use the phone number in the email, though. That is likely fake too.
Vishing
Vishing is a type of Phishing that uses voice calls instead of emails. Scammers call you pretending to be someone from your bank or any other entity that might have a reason to contact you. They try to persuade you to give them your personal or financial information over the phone or direct you to a fake website where they can steal it. The classic example is when these bums call in saying they are from Microsoft Techincal Department and there is a problem with your computer. They then try to gain your confidence to gain access to your computer.
How to protect yourself against Vishing:
- Hang up if you receive a call from an unknown number that asks you for your personal or financial information.
- Do not trust caller ID, as scammers can spoof it easily.
- Call back the official number of the entity that supposedly contacted you and verify if they called you.
- Watch Scammer Payback to educate yourself on techniques and watch these guys get what the deserve.
SMiShing
SMiShing is a type of Phishing that uses text messages instead of emails or calls. Scammers send you text messages that contain links to fake websites or phone numbers that can infect your device with malware or steal your information. These messages prey on your impulses, offering you gifts, prizes, and urgent alerts to scare you. SMiShing can also be harder to spot since you can't do things like hover over an email address or link to see if the item is a legit URL.
How to protect against SMiShing:
- Do not click on links or call any numbers from unknown senders.
- Delete any suspicious text messages from your device.
- Report any SMiShing attempts to your mobile carrier.
- Set up spam blocking on your phone.
W2 Phishing
W2 Phishing is a type of Phishing that targets employees in charge of payroll or human resources in an organization. Scammers pretend to be someone from the management team and ask for copies of W2 forms or other tax-related documents that contain employees' personal and financial information. They then use this information to file fraudulent tax returns or commit identity theft. This scam may seem like a small sample size, but hundreds can be affected very quickly with the wrong.
How to protect yourself against W2 phishing:
1) Be careful when handling sensitive documents that contain employee information.
2) Employers should ensure that anyone with access to W2 or other employee information has awareness training.
Remember, Phishing attacks try to play on your emotions like greed, panic, and trust. Here are some of the more fashionable scams used to get you to click so you can spot them in the wild:
The Nigerian Prince Scam: You receive an email from a supposed Nigerian prince who needs your help to transfer millions of dollars out of his country. Literally the oldest con on the net. The first email was sent by Ray Tomlinson in 1971. The second email was probably from a Nigerian Prince offering Ray a cut of his 10 million dollar transfer.
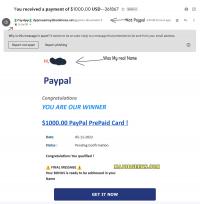
The Fake Lottery Scam: You receive an email claiming that you have won a massive amount of money in a lottery you never entered. You must pay a small fee or provide your personal information to claim your prize.
The Fake Invoice Scam: You receive an email with an attached invoice for a product or service you never ordered. The email urges you to pay the invoice quickly or face legal consequences.
The Fake Antivirus Scam: You receive an email or a pop-up warning you that your PC or phone is infected. The message directs you to download and install fake antivirus software that will harm your device and/ or steal your data.
The Fake Login Scam: You receive an email that looks like it came from a legitimate website or service that you use, such as your bank, social media, or email provider. The email asks you to click on a link and log in to your account to verify your identity or update your information. The link leads you to a fake website that will capture your username and password.
Like the wise ones say, "If something sounds too good to be true, it probably is." If something looks suspicious, don't click it. Don't reply to it. Check it out and report it if necessary.
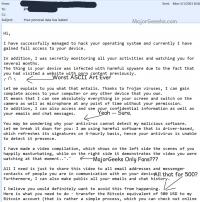
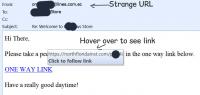
Below are some examples of Phishing that I found in my own inbox while writing so you can see what they look like. I redacted some things so people wouldn't try following the links.
Stay safe, Geeks!


comments powered by Disqus





