Change User Account Control (UAC) Prompt Behavior for Standard Users in Windows 10 & 11
By Timothy Tibbettson 06/16/2023 |
Account Control, or UAC, has been built into Windows for security to prevent changes to your computer. While Administrators can quickly get around these prompts, Standard users may need to enter additional credentials. In this guide, we look at how to change the UAC prompt for Standard users.
Depending on your operating system, we can make these changes with Local Security Policy or by editing the registry.
1: Local Security Policy
Windows 10 Pro, Enterprise, or Education can use the Local Security Policy.
Press the Windows Key + R, type in secpol.msc and press Enter. Click on Local Policies, then Security Options.
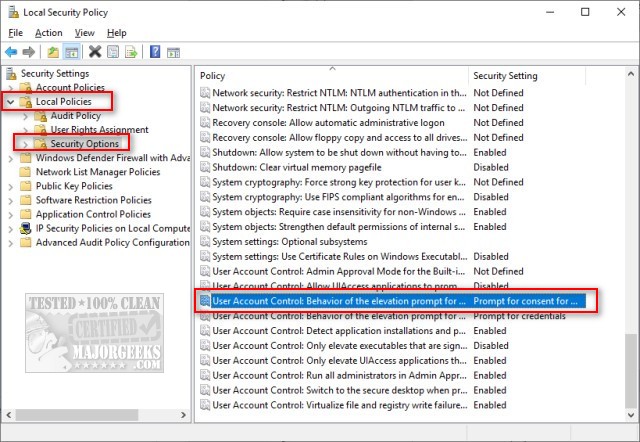 prompt behavior in windows 10 1.jpg)
On the right pane, double-click on User Account Control: Behavior of the elevation prompt for standard users..
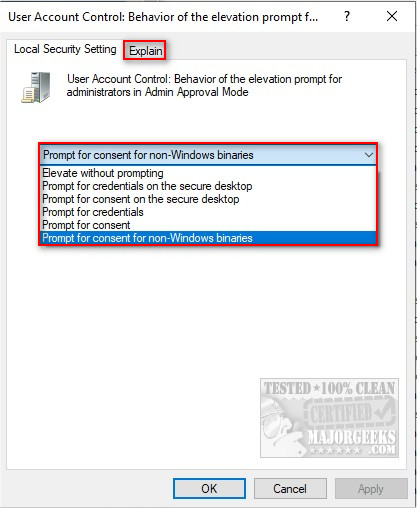 prompt behavior in windows 10 2.jpg)
Prompt for consent for non-Windows binaries is the default setting. Click on that to see your options. Elevate without prompting will disable UAC. You can also click on the Explain tab for an explanation of each setting. There are six choices:
• Elevate without prompting: Allows privileged accounts to perform an operation that requires elevation without requiring consent or credentials. Note: Use this option only in the most constrained environments.
• Prompt for credentials on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to enter a privileged user name and password. If the user enters valid credentials, the operation continues with the user's highest available privilege.
• Prompt for consent on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to select either Permit or Deny. If the user selects Permit, the operation continues with the user's highest available privilege.
• Prompt for credentials: When an operation requires elevation of privilege, the user is prompted to enter an administrative user name and password. If the user enters valid credentials, the operation continues with the applicable privilege.
• Prompt for consent: When an operation requires elevation of privilege, the user is prompted to select either Permit or Deny. If the user selects Permit, the operation continues with the user's highest available privilege.
• Prompt for consent for non-Windows binaries: (Default) When an operation for a non-Microsoft application requires elevation of privilege, the user is prompted on the secure desktop to select either Permit or Deny. If the user selects Permit, the operation continues with the user's highest available privilege.
2: Editing the Registry
Windows 10 Home or other editions which don't have Local Security Policy will need to edit the registry.
Press the Windows Key + R, type in regedit, and press Enter.
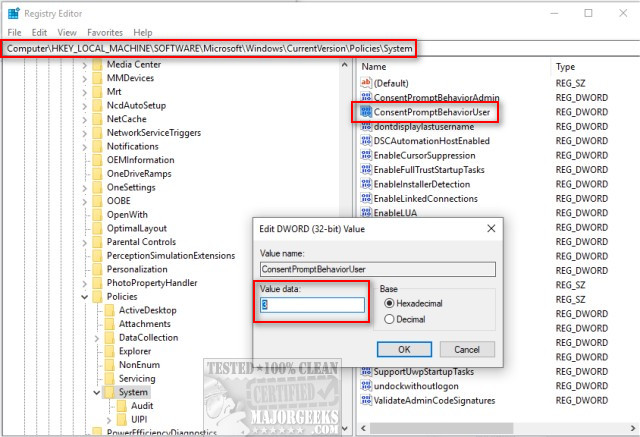 prompt behavior in windows 10 3.jpg)
Copy and paste HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System into the search bar and press Enter.
Double-click on ConsentPromptBehaviorUser. If that does not exist, right-click on a blank area in the right pane and click New > DWORD (32-bit Value) and name that ConsentPromptBehaviorUser. With the registry, there are only three choices:
0 - Automatically deny elevation requests
1 - Prompt for credentials on the secure desktop
3 - Prompt for credentials (default)
You probably noticed other UAC settings when you were exploring. These are explained here.
Similar:
How to Check if User Accounts are Administrator or Standard Users
How to Check If Users Are Local or Microsoft Accounts in Windows 10
Force Users to Change Account Password at Next Login
How to Hide Last Signed in Users in Windows 10
How to Find Security Identifier (SID) of Users in Windows 10, 8, and 7
comments powered by Disqus
Depending on your operating system, we can make these changes with Local Security Policy or by editing the registry.
1: Local Security Policy
Windows 10 Pro, Enterprise, or Education can use the Local Security Policy.
Press the Windows Key + R, type in secpol.msc and press Enter. Click on Local Policies, then Security Options.
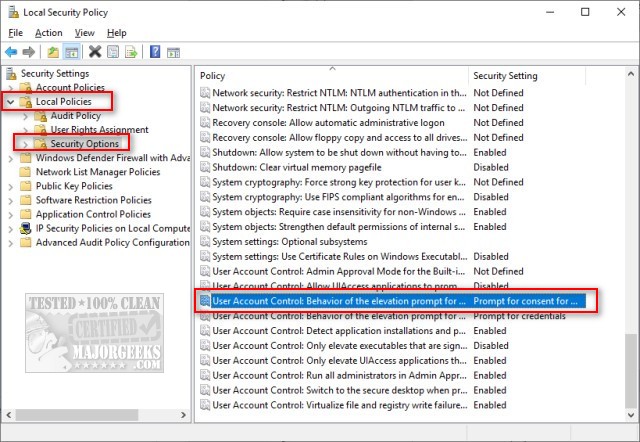 prompt behavior in windows 10 1.jpg)
On the right pane, double-click on User Account Control: Behavior of the elevation prompt for standard users..
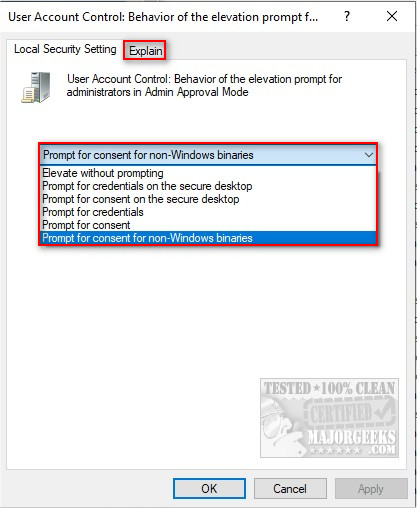 prompt behavior in windows 10 2.jpg)
Prompt for consent for non-Windows binaries is the default setting. Click on that to see your options. Elevate without prompting will disable UAC. You can also click on the Explain tab for an explanation of each setting. There are six choices:
• Elevate without prompting: Allows privileged accounts to perform an operation that requires elevation without requiring consent or credentials. Note: Use this option only in the most constrained environments.
• Prompt for credentials on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to enter a privileged user name and password. If the user enters valid credentials, the operation continues with the user's highest available privilege.
• Prompt for consent on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to select either Permit or Deny. If the user selects Permit, the operation continues with the user's highest available privilege.
• Prompt for credentials: When an operation requires elevation of privilege, the user is prompted to enter an administrative user name and password. If the user enters valid credentials, the operation continues with the applicable privilege.
• Prompt for consent: When an operation requires elevation of privilege, the user is prompted to select either Permit or Deny. If the user selects Permit, the operation continues with the user's highest available privilege.
• Prompt for consent for non-Windows binaries: (Default) When an operation for a non-Microsoft application requires elevation of privilege, the user is prompted on the secure desktop to select either Permit or Deny. If the user selects Permit, the operation continues with the user's highest available privilege.
2: Editing the Registry
Windows 10 Home or other editions which don't have Local Security Policy will need to edit the registry.
Press the Windows Key + R, type in regedit, and press Enter.
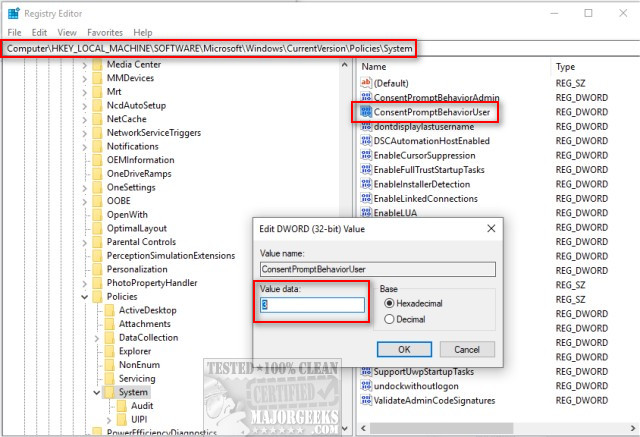 prompt behavior in windows 10 3.jpg)
Copy and paste HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System into the search bar and press Enter.
Double-click on ConsentPromptBehaviorUser. If that does not exist, right-click on a blank area in the right pane and click New > DWORD (32-bit Value) and name that ConsentPromptBehaviorUser. With the registry, there are only three choices:
0 - Automatically deny elevation requests
1 - Prompt for credentials on the secure desktop
3 - Prompt for credentials (default)
You probably noticed other UAC settings when you were exploring. These are explained here.
Similar:
comments powered by Disqus





